So serious question here. How long will people continue to actively try and bypass GV’s security/network policies for their “free service”? Along with violating GV’s ToS?
As someone who has been building/engineering SIP networks for providers/LECs for almost 15 years, GV is actively locking down their SIP network as the months roll on. Sure this is GV “working out the bugs/kinks” as some have commented but the issue here is boys and girls, kids of all ages. You are the bugs/kinks they are working out.
This latest move with TLS is another step in securing the network. Now I see the answer is to use “donated” key/crt pairs, creating a fake CA cert, setting up NAT port rules via iptables, installing/running sslsplit to make it work and the most important step: hope GV doesn’t block this.
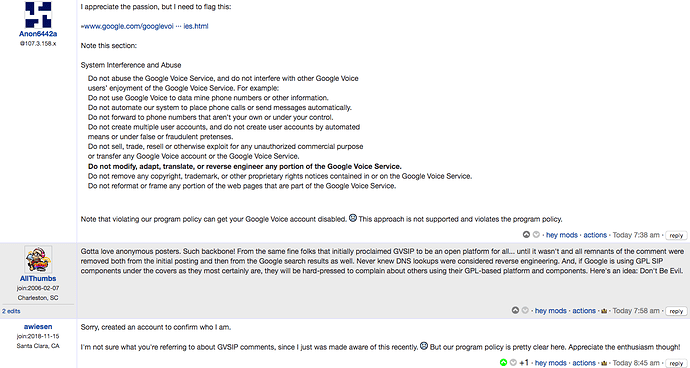
So again, how long will this go on? This has really gone from “Oh let’s see if I can make it work” to “I’m actively figuring out how to get around each new security step GV is rolling out to do things against their ToS”.