Anyone hosting on Vultr see a massive bot attack of sip overnight? My Fail2Bans have been working overtime since about 7pm eastern time US yesterday. Haven’t seen one like this in a while. API Ban on all the systems but apparently they aren’t hitting their honeypots…
Not only happens on hosting and is hard take action because attacks coming from many IP address at the same time.
I had used many years Vultr, You have to activate Vultr and FreePBX side Firewall.
Yes I have both firewalls up and am runing API Ban on all PBX’s.
This attack is unrelenting… going on 2 days now. Haven’t seen one this persistent before.
Do you see something in the httpd logs ? Like they trying to get a specific url ?
it’s all agains the SIP Ports. (Non traditional)
The deeper I dig in it also appears to be agains only a subset of my PBX’s…
The uptick might be related to attempts at exploiting some recent underlying security fixes in the PJSIP stack that are still percolating down the stream to consumers like FreePBX e.g.
This is actively being worked on internally so please expect more updates soon.
So what does that mean exactly? An asterisk version update or is this a FreePBX issue?
Both ![]()
The supply chain looks like this:
FREEPBX uses ASTERISK uses PJSIP
There were security issues fixed in PJSIP. So ASTERISK put out versions with those fixes. Then FREEPBX is incorporating said fixes as new versions of the generated ASTERISK RPM/DEB packages.
But each step in the supply chain requires QA, especially when other changes were included upstream beyond the minimal security fixes, so, it is not instantaneous.
Ok, lets try this another way… Which versions of asterisk/freepbx are vulnerable?
Everything using PJSIP. The latest certified releases and the release of 21 have backported patches. Other branches will get it with the next set of releases currently in release candidate status, should be proper releases from the Asterisk side next week. PJSIP themselves haven’t even done an official release incorporating them. All that being said… the vulnerabilities though I really don’t believe anyone is targeting and are unrelated to this. They’re not interesting enough and require either authentication or anonymous, even then you can’t easily cause them to happen due to PJSIP’s memory model.
Dumb question. I read the GitHub details. Assuming this potential vulnerability can only be exploited on unpatched PJSIP once a bad actor has SIP registered, correct? To be able to overrun the presence feature I would assume so.
Yes. You have to be authenticated.
![]() The latest certified versions of Asterisk passed internal FreePBX QA and are now available when you upgrade using the
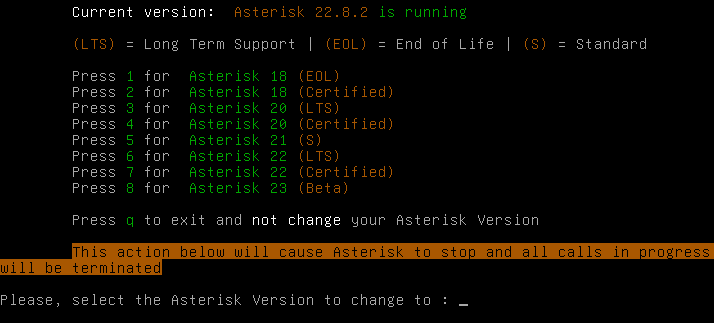
The latest certified versions of Asterisk passed internal FreePBX QA and are now available when you upgrade using the asterisk-version-switch tool on the Linux CLI (assuming here you have a recent working install of FreePBX 17 on Debian 12 that is locked to that version of the OS and there are no calls active on your system because this will cause an Asterisk process restart):
$ sudo apt update
$ sudo apt upgrade
$ sudo asterisk-version-switch
Screen shot of that last command output menu:
…after pressing a number and confirming with ‘y’, you should see output scroll by from several commands that run and shuffle around the new packages and restart various services (in case this is your first time ![]()
When done, you can run:
$ sudo -u asterisk /usr/sbin/asterisk -rx "core show version"
…which, if you chose option 7 above, should output something like:
Asterisk 22.8.2 built by jenkins @ 66cfa9b9d797 on a x86_64 running Linux on 2026-04-02 09:44:09 UTC