The weak password module doesn’t consider a 9 digit password that appends with 1234 as a weak password.
Your post is a bit confusing. Your topic has NAME1234 which would be a 4 character password with 1234 appended to it. Your post claims that a 9 digit password with 1234 is showing as secure. So while NAME1234 might not be very secure, 5918240371234 might be considered secure enough.
A 13 digit MD5 hashed password could be cracked via brute force as early as 2018 by an RTX 2080 GPU in four minutes. Asterisk 16.28.0 sip registration with PJSIP show packets using an MD5 algorithm.
A 9 character password with lowercase, uppercase, digits, and symbols can be cracked by brute force anywhere between 7 hours to 2 days (this assumes unlimited brute force accessibility before considering firewalls like RFW).
I don’t think any of the following options could be considered secure:
SOMEN1234
982311234
5918240371234
RANDO1234
If a password can’t withstand a brute force test, is it really secure?
So that module was written over 10 years ago and was primarily making sure people with extension 1234 weren’t using 1234 as a sip password or as a voicemail password for 1234. It has a few extra rules but is honestly not looking for a whole lot.
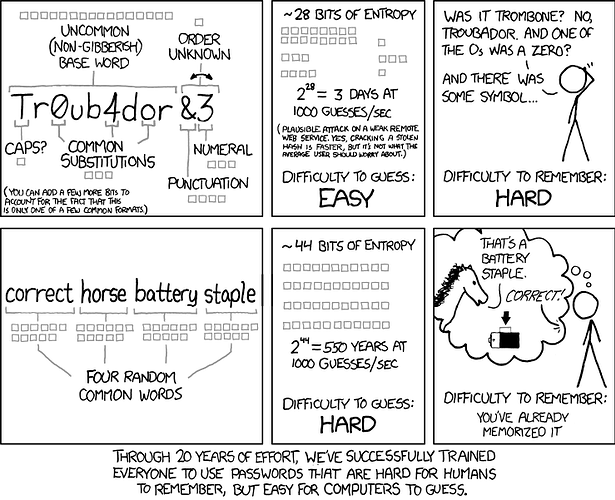
That said the industry standards for password security isn’t that great either.
About 5ish years ago we added the ZXCVBN library to the frontend to rate passwords. It was on my list to move the module over to this with a minimum rating but that was always back burnered for things that made money. I still think it would be a good idea though
That background info is helpful. Thank you.
This topic was automatically closed 30 days after the last reply. New replies are no longer allowed.