I’m asking the people with industry experience wood something like this ever happen with telnyx or bandwidth or twilio or flowroute is effective DDOS protection industry-standard
Not acceptable, ma bell is generally 99.999%
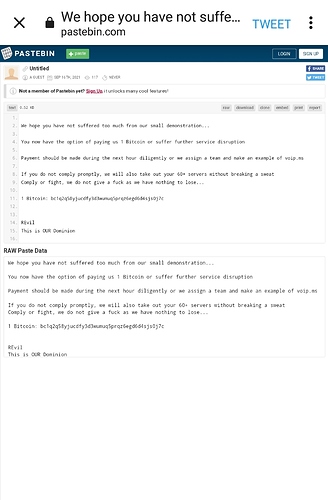
It seems like they’re helpless and trying to weather the storm
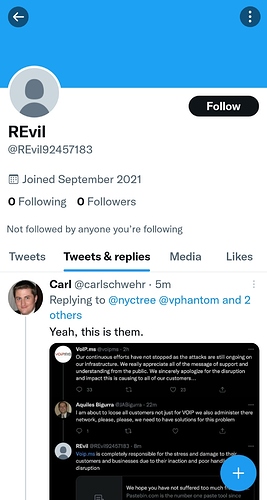
This could not happen to Bandwidth (yet), because they have enough bandwidth (pun intended) to withstand even what REvil can muster.
Telnyx, Twilio and Flowroute are much larger than VoIP.ms, though I suspect not large enough to be inherently invulnerable. However, they also have larger IT staffs to respond to issues and IMO have more resilient architectures.
For example, as I write this, access to www.voip.ms gets a 522 error from Cloudflare. Why? I suspect that their origin server is being hammered by the attackers. My opinion of Cloudflare is quite high and believe that it should be possible to hide the origin server IP address(es) from the attackers. Possibly, in addition to the DDoS, the attackers have breached security at VoIP.ms and have access to internal communications, infrastructure consoles, etc. Even if this happened at one of the other providers you mentioned, I believe that they have the human resources to quickly recover.
Xbox Live, PlayStation Network’s Online Services Suffer DDoS Attacks 6 years ago
It is interesting. As a Canadian I am watching this closely. We do NOT use them as a gateway provider, but I still think an event like this is of importance, and needs to be watched closely. Hopefully its some sort of teachable moment as well, for prevention.
Assuming this is a criminal and not a state sponsored attack, dumping them will encourage the criminals, because, even if they don’t get paid a ransom this time, it will make the next victim more likely to pay up.
Criminal or state it doesn’t matter to my clients are they missing basic protection measures against DDOS was there something that could have done to prevent this, DDOS is not new it is as old as the internet itself
They need to pay more money for their service. The basic defence against any DoS attack is to have a lot of capacity, so that the attacker cannot provide enough capacity to saturate the victim’s spare capacity. Whilst I haven’t looked at the details of voip.ms, people have said they are a small operator. That makes them vulnerable. They may well be cheap, which would be because they are small and want to attract customers, or because they are very efficient and don’t have the spare capacity to absorb an attack.
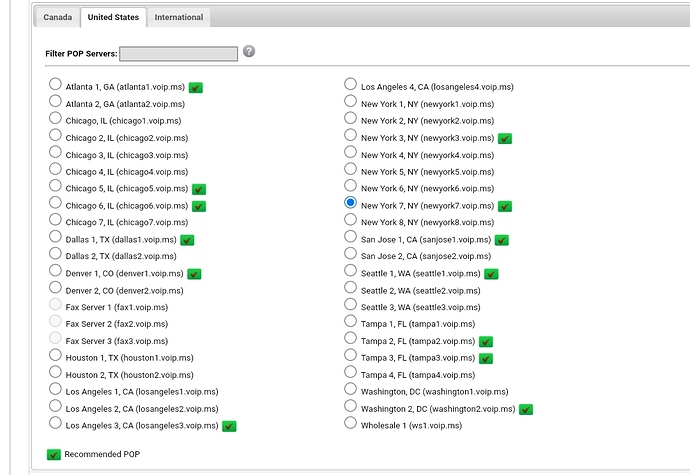
As you can see in this picture you have to manually select the server they recommend now, bigger carriers would have an option to select the region and that’s it, they would automatically distribute the load between all the servers equally, And not allow new connections too overloaded servers
I’m not really speaking ill of VoIP.ms but let us be honest here. VoIP.ms is not a big enough company that demands half of these POPs anyways. I find it highly unlikely that VoIP.ms has such a large customer presence in the NY area that they need eight POPs just for it.
The other issue I’ve seen is that VoIP.ms also has multiple cloud data center providers. Which is fine if handled properly but all their POPs are mixed between them which means there is zero consistency with their network security across all their POPs. Some may have DDoS protection tools, some may not and some may have them but you need to pony up the $$$ for them. This results in what is happening right now with VoIP.ms, a small number of POPs still functioned during all this probably due to the cloud data center provider having DDoS protection (or at least better than the others).
So I feel their infrastructure design is a bit bloated and it for sure doesn’t help situations like this.
Defending from DDoS Attacks
Doesn’t work for voip.ms yet , as of yesterday morning anyway they ARE using Cloudflare for their DNS.
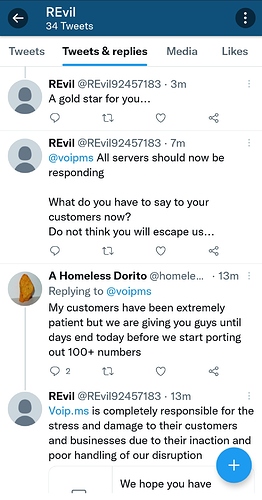
Still ongoing
Now you see me, now you don’t
…A Distributed Denial of Service (DDoS) attack continues to be targeted at our Websites and POP servers. Our team is deploying continuous efforts to stop this however the service is being intermittently affected. We apologize for all the inconveniences…
Probably a good time for all of us to make sure our own DNS are well protected from DDoS attacks before we need it. . .
They say you get what you pay for. In the case of voipms I think you get way more than you pay for. Let’s be honest. You pay damn near nothing for service and they are pretty much always up. You aren’t covering the cost of a full NoC team or security engineers. You are paying for Terry in his basement
All of there POPs host names Still Point to the same IPs