I have a simple configuration that consists of three extensions and three conference bridges. This is to allow smartphones to join a conference while in the field. There are no trunks. The idea is to allow 4-5 users conference. I have the extensions pointing to the conference numbers.
Extension 1001 >> Conference 5060
Extension 1002 >> Conference 5061
Extension 1003 >> Conference 5062
[email protected]
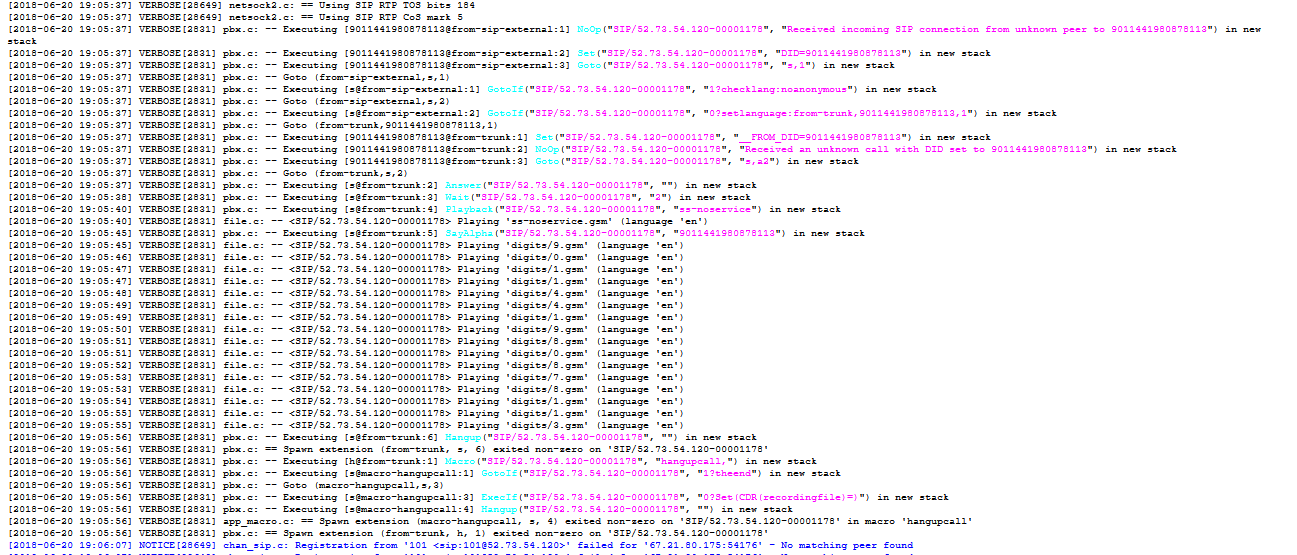
The logs indicate the connection is made to the pbx but the connection is dropped. When I look at the conference settings. I get this error
No such command 'confbridge list' (type 'core show help confbridge list' for other possible commands)
What am I doing wrong?Show us the logs and we might be able to give you a better guess, but I’d probably start with looking at RTP issues. If there’s no RTP traffic, the call will be dropped pretty quickly.
Thanks for the response. It might be a good idea to explain how we make connections to the PBX. We have a server that uses an xml file to provide users with the extension numbers that are tied to a conference bridge. Only authorized user have access to the bridge. Remote users are iphone and android smartphones with code of the conference bridge in our application
Here is a part of the code that sets up the conference bridge
<sipAddresses>
<sipAddress id="1" name="Conf_1" description="Conference 1" pin="pp12345" disabled="false" codec="Pcmu" duplex="true" colorization="FFC0CB">1001@@mypbx.FQDN.com;transport=tls</sipAddress>
<sipAddress id="2" name="Conf 2" description="Conference 2" pin="pp12345" disabled="false" codec="Pcmu" duplex="true" colorization="FFC0CB">[email protected];transport=tls</sipAddress>
</sipAddresses>
I have been able to access the pbx using Blink on a PC and get the response we expect. You are the only person in the conference.
I believe we are not getting properly registered.
thanks for looking at this
This log fragment is almost certainly unrelated to your issue. A hacker was hoping that your system was misconfigured and would interpret the 9011441980878113 as 9 (outside line) 011 (international prefix) 44 (UK) etc. and call his UK number. You system properly rejected that. Then, he (or a different hacker) tried to register an extension 101 and your system rejected that, too.
If your log is inundated with these attempts, you should secure your system better. fail2ban would be a good place to start. Changing your SIP UDP bind port from 5060 to something random is easy and would help a lot. Of course, the latter change also requires you to configure any UDP extensions to connect to the new port.
Looks like you are allowing anonymous/guest connections, DON’T do that
Another thought: Was your Blink test using TLS? It appears that your system is not listening on TCP port 5061 (standard for SIP TLS) or it’s blocked by AWS firewall or your iptables. If you are using a nonstandard port, your XML would need to pass the port number to the app.