The PBX is hosted with CyberLynk and the phones are on my local LAN. If I use my OpenVPN client on my Windows machine and request the config file it downloads without a problem. I will do some more testing, but I believe the phone downloads the config just fine, attempts to connect to the VPN, which gets an IP but disconnects.
Here are the logs from /var/log/messages
Mar 23 11:08:59 freepbx openvpn: Tue Mar 23 11:08:59 2021 x.x.x.x:61006 VERIFY OK: depth=0, CN=client24
Mar 23 11:09:00 freepbx openvpn: Tue Mar 23 11:09:00 2021 x.x.x.x:61006 [client24] Peer Connection Initiated with [AF_INET]x.x.x.x:61006
Mar 23 11:09:00 freepbx openvpn: Tue Mar 23 11:09:00 2021 client24/x.x.x.x:61006 OPTIONS IMPORT: reading client specific options from: ccd/client24
Mar 23 11:09:00 freepbx openvpn: Tue Mar 23 11:09:00 2021 client24/x.x.x.x:61006 MULTI: Learn: 10.8.0.201 → client24/x.x.x.x:61006
Mar 23 11:09:00 freepbx openvpn: Tue Mar 23 11:09:00 2021 client24/x.x.x.x:61006 MULTI: primary virtual IP for client24/x.x.x.x:61006: 10.8.0.201
Mar 23 11:09:00 freepbx openvpn: Tue Mar 23 11:09:00 2021 client24/x.x.x.x:61006 PUSH: Received control message: ‘PUSH_REQUEST’
Mar 23 11:09:00 freepbx openvpn: Tue Mar 23 11:09:00 2021 client24/x.x.x.x:61006 SENT CONTROL [client24]: ‘PUSH_REPLY,route x.x.y.y 255.255.255.128,route-gateway 10.8.0.1,topology subnet,ping 10,ping-restart 120,ifconfig 10.8.0.201 255.255.255.0,peer-id 0,cipher AES-256-GCM’ (status=1)
Mar 23 11:09:00 freepbx openvpn: Tue Mar 23 11:09:00 2021 client24/x.x.x.x:61006 Data Channel: using negotiated cipher ‘AES-256-GCM’
Mar 23 11:09:00 freepbx openvpn: Tue Mar 23 11:09:00 2021 client24/x.x.x.x:61006 Outgoing Data Channel: Cipher ‘AES-256-GCM’ initialized with 256 bit key
Mar 23 11:09:00 freepbx openvpn: Tue Mar 23 11:09:00 2021 client24/x.x.x.x:61006 Incoming Data Channel: Cipher ‘AES-256-GCM’ initialized with 256 bit key
Mar 23 11:09:01 freepbx openvpn: Tue Mar 23 11:09:01 2021 client24/x.x.x.x:61006 IP packet with unknown IP version=0 seen
Mar 23 11:10:32 freepbx openvpn: Tue Mar 23 11:10:32 2021 client24/x.x.x.x:61006 SIGTERM[soft,remote-exit] received, client-instance exiting
And the syslog from the phone itself.
[03-22 20:31:59 50:5d:67] vpn_log_file_length is 0, st_size is 0
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:41 2021 OpenVPN 2.2.2 mips-linux [SSL] [LZO2] [EPOLL] [eurephia] built on Jun 21 2014
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:41 2021 NOTE: OpenVPN 2.1 requires ‘–script-security 2’ or higher to call user-defined scripts or executables
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:41 2021 WARNING: file ‘/hlcfg/vpn/keys/sysadmin_client24.key’ is group or others accessible
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:41 2021 LZO compression initialized
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:41 2021 Control Channel MTU parms [ L:1542 D:138 EF:38 EB:0 ET:0 EL:0 ]
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:41 2021 Socket Buffers: R=[126976->131072] S=[126976->131072]
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:41 2021 Data Channel MTU parms [ L:1542 D:1450 EF:42 EB:135 ET:0 EL:0 AF:3/1 ]
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:41 2021 Local Options hash (VER=V4): ‘41690919’
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:41 2021 Expected Remote Options hash (VER=V4): ‘530fdded’
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:41 2021 UDPv4 link local: [undef]
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:41 2021 UDPv4 link remote: x.x.x.x:1194
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:41 2021 TLS: Initial packet from x.x.x.x:1194, sid=c9829b33 6231b379
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:41 2021 VERIFY OK: depth=1, /CN=FreePBX
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:41 2021 Validating certificate key usage
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:41 2021 ++ Certificate has key usage 00a0, expects 00a0
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:41 2021 VERIFY KU OK
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:41 2021 Validating certificate extended key usage
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:41 2021 ++ Certificate has EKU (str) TLS Web Server Authentication, expects TLS Web Server Authentication
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:41 2021 VERIFY EKU OK
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:41 2021 VERIFY OK: depth=0, /CN=server1
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:43 2021 Data Channel Encrypt: Cipher ‘BF-CBC’ initialized with 128 bit key
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:43 2021 Data Channel Encrypt: Using 160 bit message hash ‘SHA1’ for HMAC authentication
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:43 2021 Data Channel Decrypt: Cipher ‘BF-CBC’ initialized with 128 bit key
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:43 2021 Data Channel Decrypt: Using 160 bit message hash ‘SHA1’ for HMAC authentication
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:43 2021 Control Channel: TLSv1, cipher TLSv1/SSLv3 ECDHE-RSA-AES256-SHA, 2048 bit RSA
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:43 2021 [server1] Peer Connection Initiated with x.x.x.x:1194
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:46 2021 SENT CONTROL [server1]: ‘PUSH_REQUEST’ (status=1)
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:47 2021 PUSH: Received control message: ‘PUSH_REPLY,route x.x.y.y 255.255.255.128,route-gateway 10.8.0.1,topology subnet,ping 10,ping-restart 120,ifconfig 10.8.0.2 255.255.255.0’
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:47 2021 OPTIONS IMPORT: timers and/or timeouts modified
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:47 2021 OPTIONS IMPORT: --ifconfig/up options modified
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:47 2021 OPTIONS IMPORT: route options modified
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:47 2021 OPTIONS IMPORT: route-related options modified
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:47 2021 ROUTE default_gateway=192.168.8.1
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:47 2021 TUN/TAP device tun0 opened
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:47 2021 TUN/TAP TX queue length set to 100
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:47 2021 /sbin/ifconfig tun0 10.8.0.2 netmask 255.255.255.0 mtu 1500 broadcast 10.8.0.255
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:47 2021 /sbin/route add -net x.x.y.y netmask 255.255.255.128 gw 10.8.0.1
[03-22 20:31:59 50:5d:67] OpenVPN: Mon Mar 22 20:31:48 2021 Initialization Sequence Completed
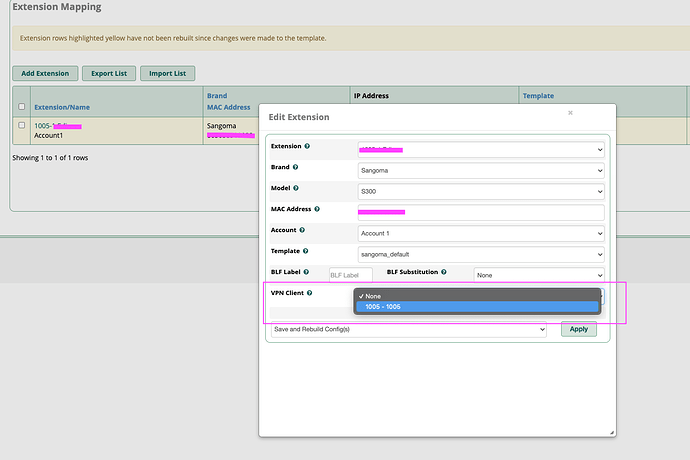
In the EPM, the phone works if I turn the VPN off (but only after deleting the config and rebuilding), as the phone will try to connect to the VPN but ultimately fails.
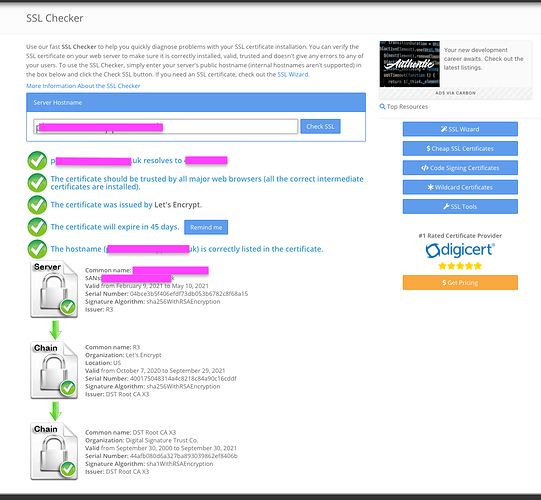
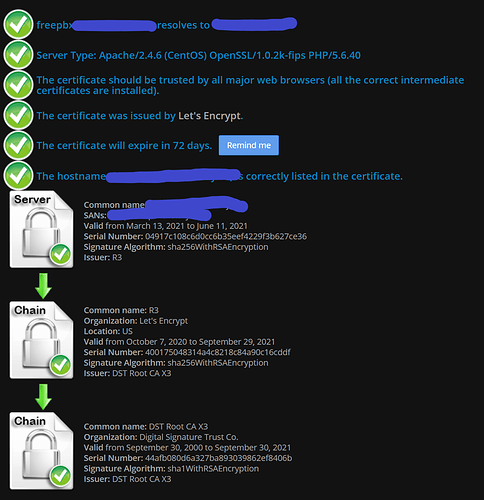
The part I find really odd is that it was working perfectly before the CERT update, at which point everything broke.