To clarify. The extension exists, but we do not use it at the moment. The password is the password Freepbx created for it.
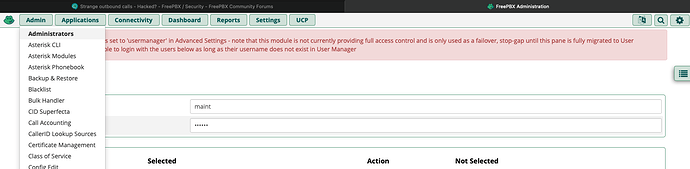
Concerning Changing password: How can I change the password for Freepbx-GUI-Login.
Attached log from the moment the call was going out:
Blockquote [2021-08-02 15:30:42] VERBOSE[8184] chan_sip.c: Registered SIP ‘502’ at 173.44.36.172:20260
[2021-08-02 15:30:42] VERBOSE[8184] chan_sip.c: Registered SIP ‘506’ at 173.44.36.172:20135
[2021-08-02 15:30:42] VERBOSE[8184] chan_sip.c: Registered SIP ‘505’ at 173.44.36.172:11661
[2021-08-02 15:30:42] VERBOSE[8184] chan_sip.c: Registered SIP ‘507’ at 173.44.36.172:13318
[2021-08-02 15:30:43] VERBOSE[8184][C-00000230] netsock2.c: Using SIP RTP TOS bits 184
[2021-08-02 15:30:43] VERBOSE[8184][C-00000230] netsock2.c: Using SIP RTP CoS mark 5
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [011442037691455@from-internal:1] Macro(“SIP/502-00000a73”, “user-callerid,LIMIT,EXTERNAL,”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:1] Set(“SIP/502-00000a73”, “TOUCH_MONITOR=1627911043.7005”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:2] Set(“SIP/502-00000a73”, “AMPUSER=502”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:3] Set(“SIP/502-00000a73”, “HOTDESCKCHAN=502-00000a73”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:4] Set(“SIP/502-00000a73”, “HOTDESKEXTEN=502”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:5] Set(“SIP/502-00000a73”, “HOTDESKCALL=0”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:6] ExecIf(“SIP/502-00000a73”, “0?Set(HOTDESKCALL=1)”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:7] ExecIf(“SIP/502-00000a73”, “0?Set(CALLERID(name)=)”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:8] GotoIf(“SIP/502-00000a73”, “0?report”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:9] ExecIf(“SIP/502-00000a73”, “1?Set(REALCALLERIDNUM=502)”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:10] Set(“SIP/502-00000a73”, “AMPUSER=502”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:11] GotoIf(“SIP/502-00000a73”, “0?limit”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:12] Set(“SIP/502-00000a73”, “AMPUSERCIDNAME=Ordination 2”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:13] ExecIf(“SIP/502-00000a73”, “0?Set(__CIDMASQUERADING=TRUE)”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:14] GotoIf(“SIP/502-00000a73”, “0?report”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:15] Set(“SIP/502-00000a73”, “AMPUSERCID=502”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:16] Set(“SIP/502-00000a73”, “__DIAL_OPTIONS=HhTtr”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:17] Set(“SIP/502-00000a73”, “CALLERID(all)=“Ordination 2” <502>”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:18] ExecIf(“SIP/502-00000a73”, “0?Set(CUSDIAL=)”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:19] ExecIf(“SIP/502-00000a73”, “0?Set(CALLERID(all)=“Ordination 2” <502>)”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:20] GotoIf(“SIP/502-00000a73”, “0?limit”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:21] ExecIf(“SIP/502-00000a73”, “1?Set(GROUP(concurrency_limit)=502)”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:22] ExecIf(“SIP/502-00000a73”, “0?Set(CHANNEL(language)=)”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:23] NoOp(“SIP/502-00000a73”, “Macro Depth is 1”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:24] GotoIf(“SIP/502-00000a73”, “1?report2:macroerror”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx_builtins.c: Goto (macro-user-callerid,s,25)
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:25] GotoIf(“SIP/502-00000a73”, “1?continue”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx_builtins.c: Goto (macro-user-callerid,s,44)
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:44] Set(“SIP/502-00000a73”, “CALLERID(number)=502”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:45] Set(“SIP/502-00000a73”, “CALLERID(name)=Ordination 2”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:46] GotoIf(“SIP/502-00000a73”, “0?cnum”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:47] Set(“SIP/502-00000a73”, “CDR(cnam)=Ordination 2”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:48] Set(“SIP/502-00000a73”, “CDR(cnum)=502”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@macro-user-callerid:49] Set(“SIP/502-00000a73”, “CHANNEL(language)=de_DE”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [011442037691455@from-internal:2] Gosub(“SIP/502-00000a73”, “sub-record-check,s,1(out,011442037691455,dontcare)”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@sub-record-check:1] GotoIf(“SIP/502-00000a73”, “0?initialized”) in new stack
[2021-08-02 15:30:43] VERBOSE[60167][C-00000230] pbx.c: Executing [s@sub-record-check:2] Set(“SIP/502-00000a73”, “__REC_STATUS=INITIALIZED”) in new stack
…
[2021-08-02 15:30:44] VERBOSE[60218][C-00000232] bridge_channel.c: Channel SIP/trunkDIC43422529888-00000a78 joined ‘simple_bridge’ basic-bridge <6ff2818b-2a53-4d6e-8a72-8ba25eb52697>
[2021-08-02 15:30:44] VERBOSE[60175][C-00000232] bridge_channel.c: Channel SIP/507-00000a75 joined ‘simple_bridge’ basic-bridge <6ff2818b-2a53-4d6e-8a72-8ba25eb52697>