We will add it for help indeed.
And I think it also loads the CPU if too many IP addresses are set in iptables by the hundreds or by the thousands.
The best way, is to set the right rules to accept instead to set bad rules to reject
I agree, I need about a dozen accept rules for mail, dns, ntp, icmp, ssh, voip, your https port , and a couple more, any drop rules are generated by the various fail2ban jails via ipsets, but even voipbl ,nearly 200000 hosts, if using ipsets is not a problem if you feel the need to expose 5060.
There are also a few rules to identify and ban port scanning and port flooding (by adding the whole underlying subnet to an ipset)
Looks like a great improvement, nice work
Hi Daniel.
I fixed that.
I just need to test it before to publish it on edge.
The page I.D will be back on sysadmin when the firewall will be disabled.
Hi @danardf,
Thank you very much for the fix.
It will help to keep the stability of systems that do not use the firewall module.
Daniel Friedman
Trixton LTD.
Great work @danardf,
Will this pickup custom jails that I have created myself with fail2ban outside of FreePBX?
Thanks ![]()
All rules / jails set are scanned
so:
# fail2ban-client status
Status
|- Number of jail: 7
`- Jail list: apache-tcpwrapper, recidive, ssh-iptables, apache-badbots, pbx-gui, asterisk-iptables, vsftpd-iptables
if there’s other jails into this list, it should work.
Nice work with the firewall update but sadly, I’m still seeing authenticated users being blocked by some combination of the firewall and fail2ban. We’re entirely softphone based (microsip) if it makes a difference.
Checking the logs I can see the address authenticated successfully: “reported as good adding to white list” but then after some period they get dropped and then end up on the banned list. Is it possible to detect successful authentications and then white list for a set minimum time? - i.e a day? this would capture most of our users as they turn there machines on and off.
slightly unrelated but since updating the firewall the log is full of php notice’s about undefined properties:
“HP Notice: Undefined property: stdClass::$id_service in phar:///var/www/html/admin/modules/firewall/hooks/voipfirewalld/firewall.php on line 9” is this an issue?
I installed the edge modules but I dont use sangoma firewall and it stopped me from being able to see fail2ban in sysadmin.
Please note not everyone uses sangomas firewall. I know you guys noted this above but please dont push to stable without fixing this.
You can get the sysadmin Intrusion Detection features back provided the firewall module is installed. You don’t have to actually turn it on tho.
it is true, but it makes hacker life a little bit more complex… Before to start to try to hack your system, they need to know which IP countries you allow.
Synology network hard disk use that , and it catches really a lot of hackers with this simple security
I think of geoblocking more as proactive log and load maintenance vs real security. Thousands of attempts dropped quickly and silently, making what’s left easier to manage.
System needs to be secure with or without geoblocking in place.
I’m not sure to which of my posts you agree with, but my gist is:-
I am saying basically geoip is not useful because , well it’s not, I as a non knuckledragger black-hat can buy a vm in your backyard for 3 euros
VOIP blacklists ONLY have hosts who use UDP/5060 so don’t use UDP/5060 and your blacklists are mostly a waste of time.
Your IP:port can be scanned trivially, but if you don’t reply to 5060 (and block it on an earlier firewall if you don’t want the noise), you reduce your visibility significantly , if you only accept REGISTER and INVITE to your domainname:unlikelyport your erstwhile hacker has even greater complexity .
So, I would suggest you use TLS:5061 with an obscure and unrelated to your internet facing domain certificate and use ‘enforced SNI’ and I believe you are close to being ‘very armored’ .
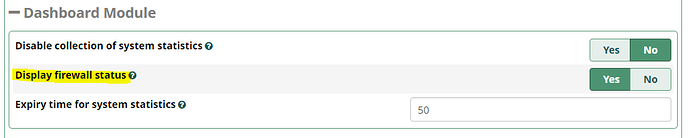
I can’t find where it was discussed recently, but there was a feature request to allow admins to suppress the dashboard notification when the PBX firewall module is installed to allow Intrusion Detection features in Sysadmin, but the firewall is not running. In dashboard versions 14.0.13, 15.0.9, and 16.0.5 there is an advanced setting to control this:
This topic was automatically closed 31 days after the last reply. New replies are no longer allowed.