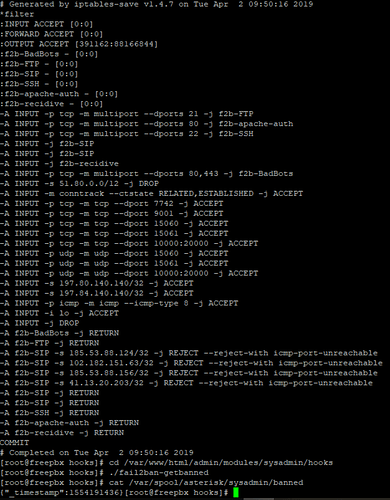
Hi. I have FreePBX 13.0.195.26 installed and I broke the fail2ban months ago trying to get the firewall working. I finally got some time to look at this and I have fail2ban (intrusion prevention) working now and it’s blocking ip’s as seen below but these ip’s are not showing up in the GUI under intrusion prevention. Referring to this post Sysadmin GUI Problem i am posting my results in hopes someone can help me resolve this. As can be seen below my hook is not pulling “SIP”:[“1.2.3.4/32”]
Sysadmin version is 13.0.87
Rob Thomas @xrobau wrote the original firewall code for FreePBX 13, which it appears you are running.
Important things to know:
-
The code in 13 was the original, first-draft, let’s-try-it-and-see-what-breaks code. It wasn’t as robust as one would hope and didn’t have many of the features that the newer code is running.
-
We are on FreePBX 15. You might be a little behind on your updates. Newer versions of the code allow you to add custom rules to the firewall, meaning you don’t have to mess with the firewall directly as often.
Hopefully Rob is watching out.
There are no fundamental differences between Firewall in 13 vs. 14. Intrusion detection and fail2ban have nothing to do with the Firewall module.
Which is super annoying. I wish intrusion detection would at least read the trusted information from the Firewall settings. Nothing like getting the entire office locked out because a phone freaks out and spews bad registrations.
One has to think about this philosophically, If you want to stop bad actors, then you can help with fail2ban , if you have your own bad actor, then you have a catch 22 , if you don’t trust your own network,then you can “ignore” that network in fail2ban, but isn’t that avoiding the issue?, just stop the phone “freaking out”, it is yours to control, no?
Sure, once the phone is known to be a problem. In the mean time the entire office is locked out.
Think about a host solution. In the firewall module I can add a FQDN using a dynamic DNS service for the office because they don’t have a static IP.
But I cannot do that for Intrusion Detection.
The worry about a bad actor inside the network is significantly less than the problem of the office losing phone service because a device fails.
Then just don’t trust your network and add the exclusion to fail2ban , when you eventually get control over your network, remove the exclusion.
If you have a rogue network that is dynamic, then I suggest you might have to allow the whole underlying network. use whois and identify either the CIDR or the “network range”. Not ideal but usable and you are only allowing comcast or your some-such provider which generally are not hosting the bad guys
This topic was automatically closed 7 days after the last reply. New replies are no longer allowed.